In the world of wireless security testing and IoT development, most tools fall into two categories:
WiFi testing devices
USB-based penetration tools
But very few combine both.
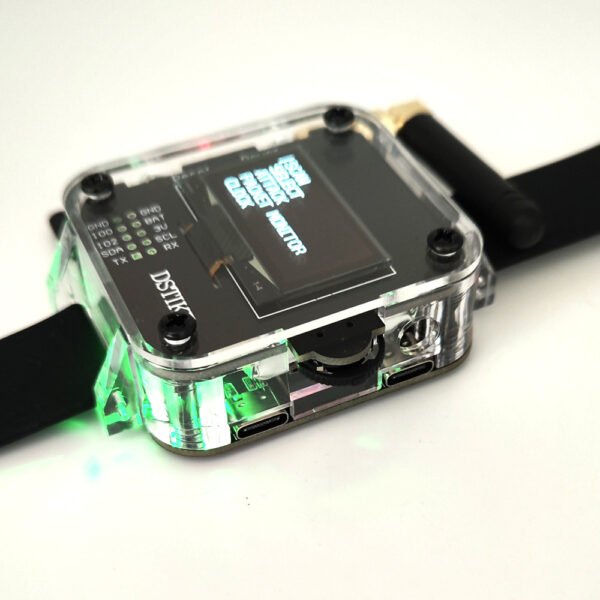
That’s where the Deauther Watch Z stands out — a compact device that merges WiFi packet-level interaction with BadUSB automation capabilities in a single platform.
🧠 What Is Deauther Watch Z
The Deauther Watch Z is a portable development and testing device built around two microcontrollers:
ESP8266 → WiFi communication & packet interaction
ATmega32u4 → USB HID (BadUSB functionality)
This dual-chip architecture allows it to function as both:
✔ a WiFi testing tool
✔ a USB automation / HID injection device
According to product-level technical descriptions, it supports features like:
WiFi scanning and packet monitoring
deauthentication frame transmission
probe request simulation
BadUSB script execution
👉 In simple terms: it’s a multi-function embedded security testing platform
📡 Understanding the Core: ESP8266 WiFi Packet Control
The ESP8266 is widely used in embedded systems because it allows low-level WiFi frame interaction, which is not typically available in standard consumer devices.
Historically, projects like ESP8266 Deauther demonstrated that:
the chip can send raw WiFi frames
simulate network behavior
interact with access points at protocol level
Practical capabilities include:
scanning nearby access points
analyzing signal strength (RSSI)
sending management frames (like deauth packets)
monitoring WiFi traffic patterns
👉 This is why ESP8266 remains popular in WiFi security research tools
🔌 The Second Layer: ATmega32u4 & BadUSB Functionality
The second core component, ATmega32u4, enables a completely different category of functionality.
It allows the device to:
emulate a USB keyboard
execute predefined scripts automatically
interact with systems via HID interface
This is commonly referred to as a BadUSB attack model, where the system trusts the device as a legitimate input source
Example use cases:
automated command execution
penetration testing simulations
security awareness demonstrations
👉 This makes the device useful beyond WiFi — into endpoint security testing
⚙️ Why Dual-Function Tools Are Increasing in Demand
Modern security environments are no longer isolated.
You often need to test:
wireless networks
endpoint vulnerabilities
IoT device behavior
Instead of carrying multiple tools, devices like this combine:
WiFi interaction
USB automation
portable testing interface
👉 This aligns with growing demand for:
portable penetration testing tools
ESP8266 security development boards
BadUSB programmable devices
🛠️ Real Use Cases
This type of device is commonly used for:
esp8266 wifi security testing tool
portable penetration testing device
badusb programmable development board
WiFi packet monitoring device
IoT security testing hardware
🧩 How It Actually Works (Simplified Workflow)
A typical usage scenario:
Step 1: Power on device
The system boots into the firmware interface.
Step 2: Select WiFi mode
Options may include:
scanning
monitoring
packet interaction
Step 3: Analyze the environment
View available networks and signal data.
Step 4: Run test scripts
Via onboard interface or USB HID scripts.
Step 5: Evaluate results
Used for debugging, testing, or learning purposes.
⚠️ Limitations You Should Know
From both documentation and user discussions:
Works primarily on 2.4GHz WiFi networks
Limited effectiveness on modern secured networks
newer standards (like WPA3) reduce vulnerability
👉 Example from community experience:
“only works on 2.4ghz… newer networks aren’t affected”
👉 Translation:
This is more of a learning and testing tool, not a universal solution.
⚖️ Legal & Ethical Use (Required, otherwise your account may be penalized)
Devices like this are designed for:
✔ education
✔ lab testing
✔ authorized network analysis
Not for unauthorized interference.
Official descriptions clearly emphasize that usage should comply with local laws and be limited to controlled environments
🔗 Recommended Product
If you want to explore this type of dual-function device, you can check:
👉 https://fixparthub.com/product/deauther-watch-z-esp8266atmega32u4-wifibadusb-hacker-watch/
This model features:
ESP8266 WiFi module
ATmega32u4 BadUSB support
SD card for script storage
portable watch-style design
Suitable for:
✔ IoT developers
✔ Security learners
✔ penetration testing practice
The Deauther Watch Z isn’t just a “gadget” — it’s a learning platform for wireless and hardware-level security concepts.
It represents a shift toward:
compact security tools
multi-function embedded devices
hands-on cybersecurity learning
If your focus is:
understanding WiFi protocols
experimenting with IoT security
learning USB-based attack vectors
then this type of device offers a practical and accessible starting point.
🚀 Final Thoughts
Deauther Watch Z | ESP8266+ATmega32u4 WiFi+BadUSB Hacker Watch
Deauther Watch Z is a multifunctional development and testing device combining ESP8266 WiFi capabilities with an ATmega32u4 microcontroller for extended USB-based applications. Designed for advanced users, developers, and hardware enthusiasts, it provides a versatile platform for exploring wireless communication, firmware customization, and embedded system integration.
With its dual-chip architecture, the Watch Z supports both WiFi-based development and USB interaction, making it suitable for a wide range of IoT projects, prototyping tasks, and technical experiments. The compact and portable design allows users to carry out testing and development conveniently in different environments.
Ideal for learning, development, and research purposes, the Deauther Watch Z offers flexibility and expandability for users who want to explore both wireless technologies and USB-based functionalities in a single device.